If there is a performance cost for this, hopefully it isn’t too high given the limited resources of the Deck.
The headroom required for the mitigation is statistically insignificant according to the details page on the cve.
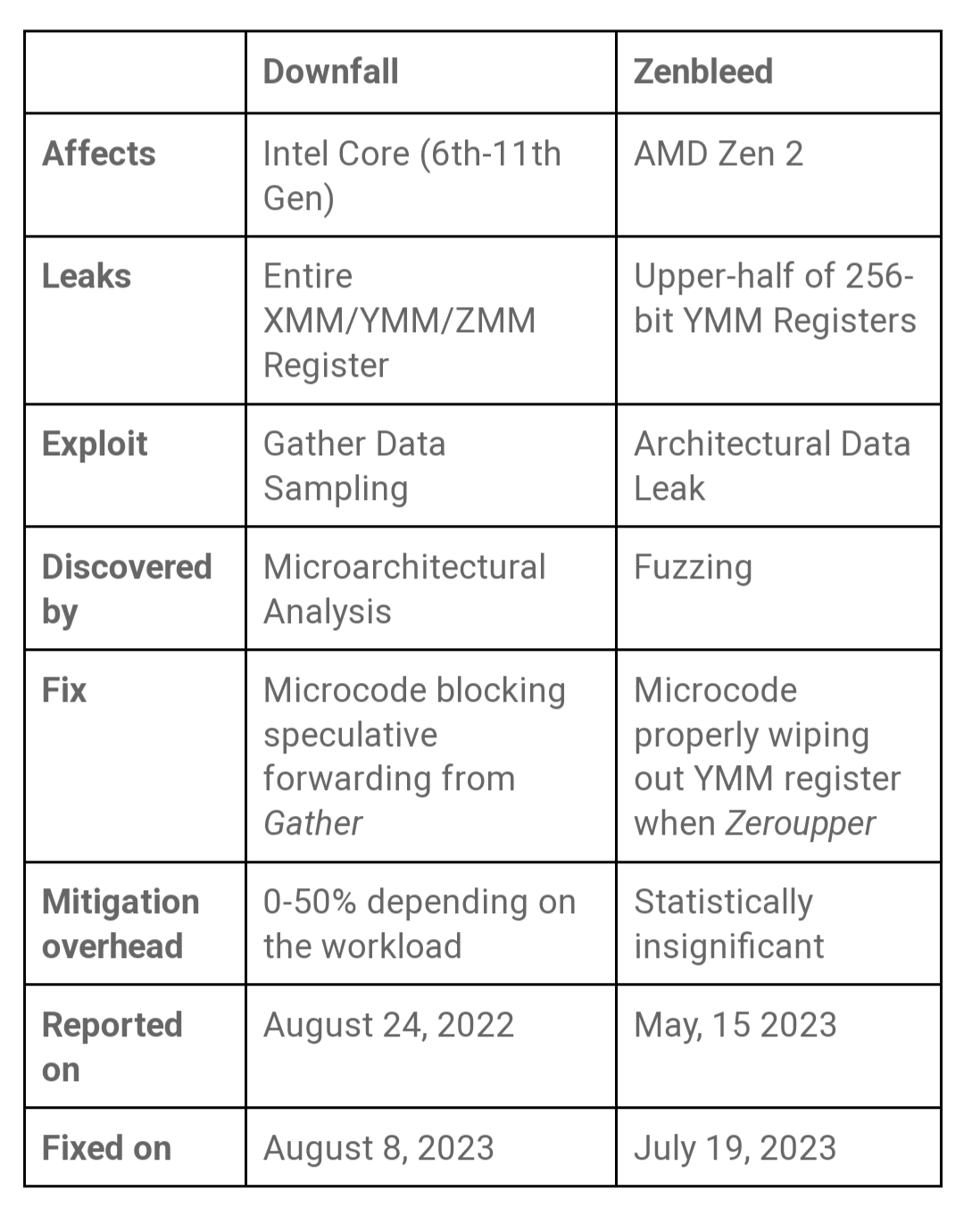
Good to see. That seems to have been the case with most of the AMD vulnerabilities actually. Which stands in stark contrast to the “up to 50%” hit of Intel’s Downfall, and some of the other Intel vulnerabilities.
This is the best summary I could come up with:
Last month when the Linux kernel was mitigated for Zenbleed as a CPU vulnerability affecting AMD Zen 2 processors, it turns out the Steam Deck APU was accidentally left without coverage.
An x86/urgent pull request sent out today for the Linux 6.5 kernel and for back-porting to current stable Linux kernel releases will extend the Zenbleed mitigation to protect Steam Deck gamers.
Most notable with these fixes is adding models 0x90-0x91 to the range of AMD Zenbleed-affected Zen 2 processors.
It looks like the Steam Deck’s custom APU was just accidentally left out in the original Zenbleed patch.
This patch enables the Zenbleed fallback fix until a proper CPU microcode update is available for the Steam Deck.
Zenbleed (CVE-2023-20593) was disclosed last month after this data leakage vulnerability was discovered by a Google researcher.
I’m a bot and I’m open source!


